Evaluation of the Cyber AI Hub - interim process evaluation
Published 11 March 2026
1. Introduction
Context
In November 2023, The Department for Science, Innovation and Technology’s (DSIT’s) Cyber Security Programme Delivery Team commissioned Steer Economic Development (Steer-ED) to conduct a comprehensive evaluation of the Cyber-AI Hub Programme (the Programme), which is being delivered in Northern Ireland by Queen’s University Belfast (Queen’s) between 2023 and 2027.
The evaluation is determining how the Programme and its four components– the Cyber-AI Technologies Hub, the Centre for Secure Information Technologies (CSIT) Doctoral Training Programme, NICYBER2025 Masters Bursaries, and The NI Cyber Security Snapshot – have performed over the period of programme delivery. The study comprises three reinforcing strands:
- An ongoing review of Programme delivery to provide learning to help shape and develop future iterations of the intervention;
- The development and implementation of a data collection plan, to monitor outputs/outcomes delivered by the Programme (including post-evaluation) to understand the ongoing benefits of the initiative for beneficiaries and participating companies; and
- An assessment of the extent to which the Programme has achieved its objectives; the impact of the Programme, and any unintended outcomes realised; and the Value for Money achieved.
The Cyber AI Hub Programme
Background and context
In 2023, at the launch of the Programme, Northern Ireland’s (NI) economy produced £51.5 billion of economic output or Gross Value Added (GVA) per year, across 920,000 jobs. Productivity in NI has persistently lagged behind the UK average. When measured by output per hour worked, productivity in NI was £38.90 per hour in 2023, around 12.5% below the UK average.[footnote 1] The Total Early-stage Entrepreneurial Activity (TEA) rate in NI was 6.5% (well below the UK rate of 7.9%), and the number of firms that were ‘innovation active’ in NI was decreasing, from 45% in 2014 to 32% in 2018.[footnote 2]
In this context, the cyber security sector is seen as having a key contribution to improving Northern Ireland’s innovation levels and productivity.
The sector has seen strong growth in recent years, with employment increasing from 1,700 in 2019 to over 2,700 in 2025 according to the latest NI Cyber Snapshot report.[footnote 3] Although growth has slowed in recent years, the sector now contributes £258 million of direct GVA to the economy and Northern Ireland remains a global hotspot for cyber security activity. The Snapshot also notes that productivity and advertised salaries remain strong, emphasising the role the sector is playing in improving innovation and productivity.
Programme overview and objectives
The Programme is being delivered by Queen’s over three and a half years, from 2023 to 2027. ‘New Deal for NI’ funding is contributing £10.4 million, and a further £4.5 million is being provided by the partners involved in delivering the Programme.[footnote 4]
The overall goal of the Programme is to grow the NI cyber security sector and substantially increase the talent pool of cyber-AI professionals in Northern Ireland by meeting the following high-level objectives:
Figure 1.1: High level objectives for the Cyber AI Hub Programme, 2023-2027
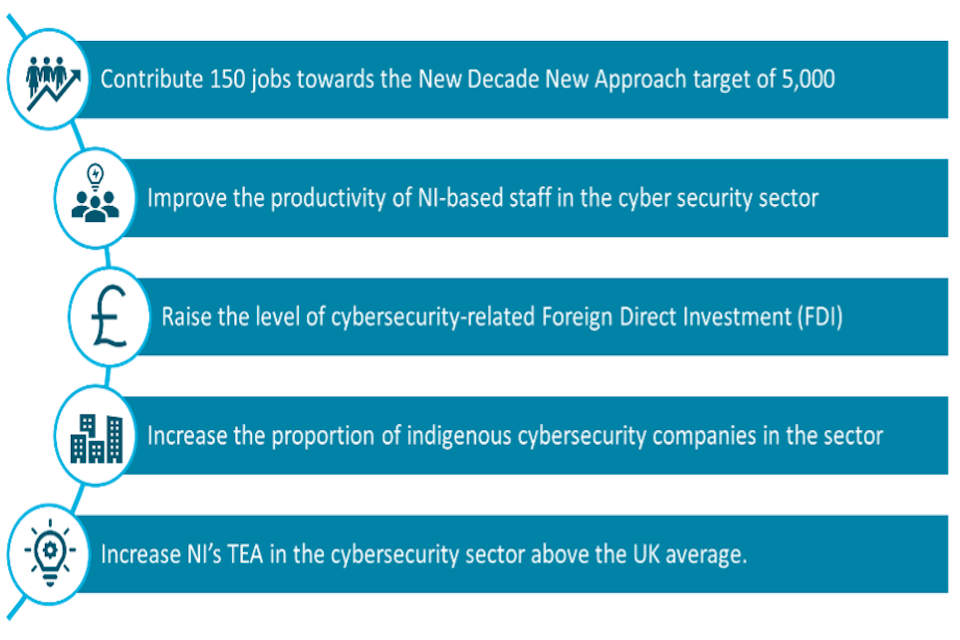
Source: Steer-ED, 2025, drawing on Cyber-AI Hub Business Case
To achieve these objectives, the Programme is delivering four interrelated strands of activity, which are summarised below.
Figure 1.2: Overview of The Cyber AI Hub Programme and its component parts
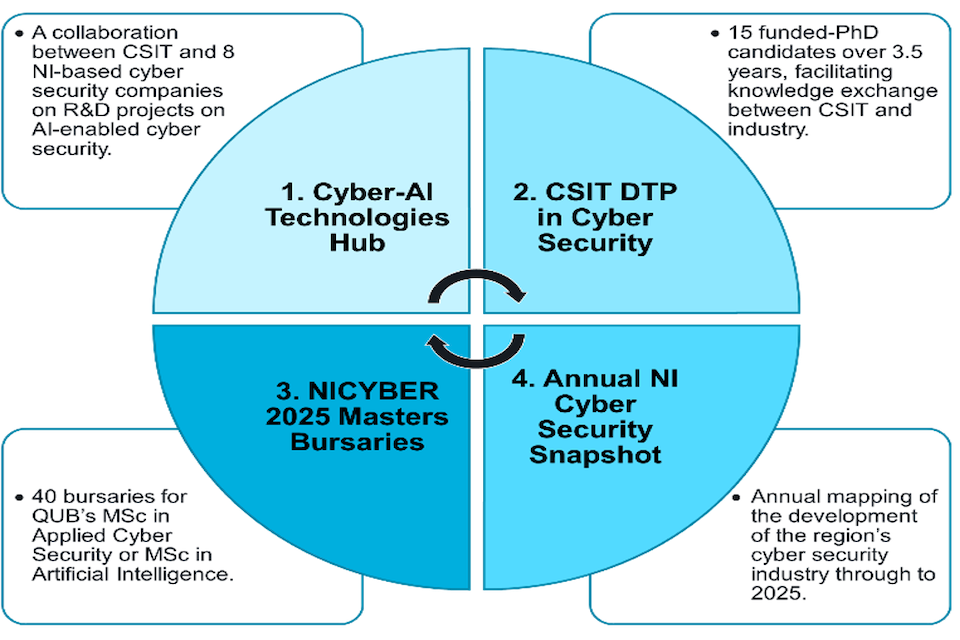
Source: Steer-ED 2025, drawing on CSIT programme documentation
The Cyber-AI Technologies Hub (the ‘Technologies Hub’)
The Technologies Hub supports collaborative projects between academia (Queen’s) and NI-based cyber industry businesses, with a particular focus on the use of AI in cyber security. The agreed projects and their aims are set out in Annex A. The Technologies Hub aims to work with eight projects contributing to objectives including creating 150 jobs, improving competitiveness for beneficiaries, and improving the long-term capacity of the NI cyber security ecosystem.
The CSIT Doctoral Training Programme (DTP) in cyber security
This strand is supporting a cohort of 15 industry-facing PhD students, including through an enhanced stipend of £27,000 per annum. The CSIT DTP has four strategic objectives, namely to:
- Produce a cohort of industry-conscious thinkers and leaders who will influence the roadmaps of cyber security technologies and their applications;
- Produce world leading scholarly output and impact through supervision from the academic team at CSIT;
- Address challenges that are strongly relevant to industry and society through partnerships and close interaction between students, industry and government stakeholders; and
- Conduct responsible research and effective innovation in the field by encouraging ethical and society-focused exploration of emerging cyber security technologies and challenges.
It is intended that there will be collaboration and knowledge sharing between the PhD students and the Cyber-AI Technologies Hub, both informal and formal, such as industry placements. Post Doctoral Research Assistants and Engineers will have opportunities work on the Technologies Hub projects.
The NICYBER2025 Masters Bursaries
This third component of the Programme is providing a bursary to 40 students to undertake master’s degrees in Applied Cyber Security (ACS) or Artificial Intelligence (AI). The objective of the bursaries is to help ensure a sustainable pipeline of talent to support continued sector growth in Northern Ireland, including educating talented high-value cyber security professionals, as well as opportunities for career retraining and apprenticeships for those employed in sectors with similar skill sets.
The Northern Ireland Cyber Security Snapshot
The final component of the Programme involves CSIT procuring an annual NI Cyber Security Snapshot (the ‘Snapshot’). The Snapshot maps the growth and development of the NI’s cyber security industry through to 2025. This information is intended to be used to track progress in the sector over the Programme’s delivery period, and as an adjunct will also provide contextual evidence from businesses for use in this evaluation’s impact assessment phase.
What the programme’s evaluation covers
The evaluation of the Programme will help DSIT understand the impact of the Cyber-AI Hub Programme (as a whole and at the level of its component parts), how Government intervention can help grow the cyber security ecosystem, and any policy considerations around this. The work will provide DSIT a robust and independent evaluation of the Programme’s added value and relevant learning on the process of implementation for both government and the private sector.
The Programme’s evaluation is being delivered over five key ‘phases’, summarised in Figure 1.3. This document comprises ‘this report’, providing the interim process and emerging outcomes evaluation, following on from last Autumn’s Phase 2 report;[footnote 5] the Phase 2 report provides more detail on the approach to the evaluation and context around the Programme which, for brevity, is not repeated here.
Figure 1.3: Sequencing of the Cyber AI Hub Programme Evaluation
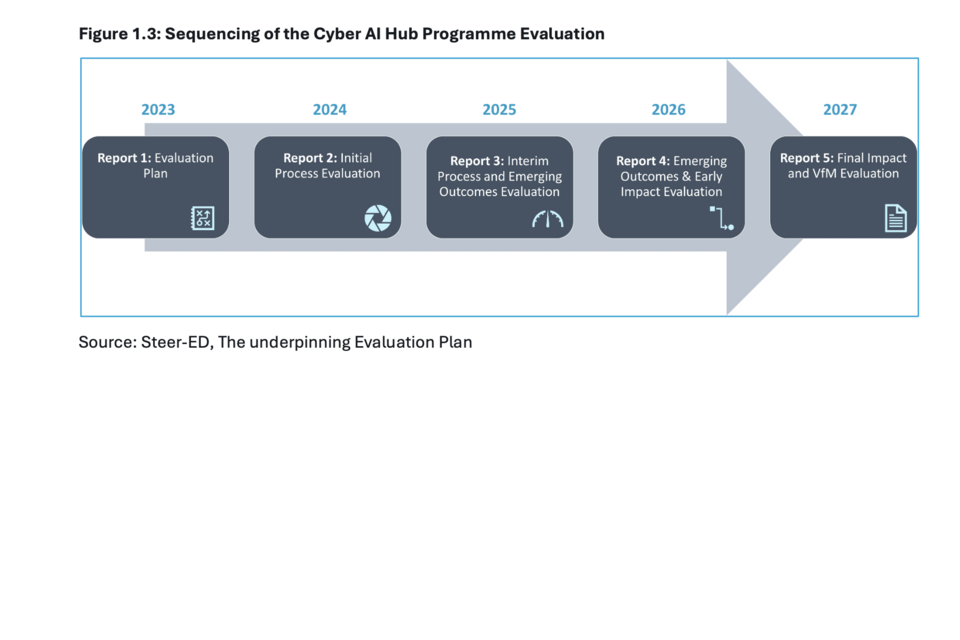
Source: Steer-ED, The underpinning Evaluation Plan
The Evaluation Plan for the Programme was developed following the study’s commissioning in early 2024 to guide the parallel assessment of the initiative’s implementation, impact, and value for money.
The Evaluation Plan is reported to DSIT as a separate document, and updated annually to reflect learning as evaluation fieldwork progressed. Building on the findings of Report 2 in 2024 (i.e. the initial Process Evaluation), the ‘base’ Evaluation Plan was updated to account for the then learning to date.
Following conclusion of this interim Process Evaluation report, the Evaluation Plan will again be reviewed in December 2025 to reflect learning from this year’s process evaluation, and as the challenges in planning for the forthcoming impact and Value for Money (VfM) workstreams come into view for Phases 4 and 5.
The approach for this interim process report
The following strands of fieldwork were undertaken between April and September 2025:
- In-depth analysis of Programme data and documents
- Detailed analysis of internal Programme data, including Innovate UK (IUK) Quarterly Monitoring Reports, the notes from the Quarterly Programme meeting, Programme financials, and other relevant documents, such as technologies Hub project overviews;
- Interviews with Cyber-AI Hub Programme delivery teams
- Semi-structured interviews were undertaken with seven representatives from the Programme Delivery Team, including at Queen’s, IUK, and DSIT. The interviews, some of which were conducted with multiple stakeholders at once, covered themes such as Programme design, delivery progress, management, and governance. Where appropriate, the questions were tailored to the four Programme components;
- Interviews with strategic stakeholders
- Semi-structured interviews were undertaken with nine strategic stakeholders from government agencies, sector/cluster bodies, and others involved with, or adjacent to, the Programme. The interviews sought to gather perspectives on programme delivery, including project set-up, collaboration arrangements with academics, engagement with CSIT and wider stakeholders, and management and governance processes. They also begun to explore areas where the Programme may already be delivering impact.
- Case studies with two Technology Hub businesses
- Semi-structured interviews with two representatives from each of the case study firms covered in this report (Rapid7 and Pytilia), and two principal investigators for each project.
The evidence generated from the research was analysed and triangulated to inform the findings and conclusions of this report. An internal workshop was also held by the Evaluation Team to support the synthesis of findings across the three research strands.
Structure of this report
This report is structured as follows:
- Chapter 2: Overview of Programme Progress – provides a summary of developments with each Programme strand since last year’s Report 2;
- Chapter 3: Process Reflections – presents findings on the Programme’s interim implementation and management;
- Chapter 4: Evidence of Early Outcomes – identifies areas where, at this early stage, there is evidence of the Programme delivering early outcomes and impacts; and
- Chapter 5: Conclusions and Recommendations – synthesises the key findings from Chapters 2 to 4 and makes recommendations for the remainder of the Programme and future phases of the evaluation.
There are two annexes:
- Annex A: Summary of Technologies Hub projects – provides an overview of the aims of projects in the Technology Hub, recent progress and next steps
- Annex B: List of consultees – provided details of those individuals who were consulted in the course of producing this report.
2. Programme progress
Purpose
This chapter presents developments on the Programme and its constituent strands since the publication of the previous report (Report 2) in Autumn 2024. It provides a summary of activity across each strand, and considers spend against the anticipated profile.
For the programme as a whole
Headlines
Overall, the Programme has progressed effectively over the past year. At the time of the last report the Technologies Hub had been working to overcome challenges in mobilising collaborative projects, due to issues relating to subsidy control. These issues have now been overcome and projects are progressing, though there has been some churn in the companies engaged with the Hub.
Both the PhD and MSc strands have recruited successfully in their initial cohorts, although both have seen a small number of participants drop out. Recruitment for the MSc programme has been split across four academic years of entry, and is now fully occupied.
The Snapshot has now delivered two iterations of its report with a third in draft as of November 2025.
An overview of progress across the Programme components is set out in Table 2.1.
Table 2.1: Overview of progress by strand
| Programme component | Output/KPI | Target | Notes of progress | Overall status |
|---|---|---|---|---|
| Cyber-AI Technologies Hub | Number of collaborative projects Number of useful cyber technologies, processes or MVPs produced |
8 5 |
• Five collaborative projects are currently active, though there have been some changes to participants. Four participant firms have left the Programme, though three produced tangible outputs (two MVP, one PoC). A new collaborative project began in March 2025. • Discussions ongoing with potential partners and two Phase 2 extensions. • Team anticipates one output per project, totalling eight. |
Delayed (7–8 months) but on target overall. |
| CSIT DTP in cyber security | PhDs recruited/completed | 15 | • 15 enrolled • 14 passed Differentiation • 2 withdrawn |
Progressing well but max 13 graduates expected |
| NICYBER 2025 Masters Bursaries | Masters recruited/completed | 40 | Cohort 1 • 20 enrolled • 13 graduated • 5 progressing • 2 withdrawn Cohort 2 • 14 FT + 1 PT enrolled • 12 MSc grads, 3 PGDip, 1 PGCert • 3 resits in 25/26 Cohort 3 • 7 MSc starting Sept 2025 |
Slower recruitment but near target |
| NI Cyber Security Snapshot | Annual Snapshot | 3 | • 2023 published • 2024 published Q2 24/25 • 2025 draft delivered Nov 2025 |
On track |
Source: Steer-ED analysis of Queen’s Monitoring Data, 2025
Programme spend
Due to initial (but now resolved) subsidy control issues and changes in participant recruitment timelines outlined above, the profile of Programme expenditure has been amended. Monitoring reports from July 2025 indicate that spend for financial years 2022/23 and 2023/24 was largely in line with the profile set out in September 2024 at the Programme level.
However, there was variation by strand. Spend on the PhD and MSc components was £510,000 lower than forecast in 2023/24, but this was offset by spend on Technologies Hub being higher than forecast by a similar amount (£530,000). Spend on the Technologies Hub was subsequently less than forecast in 2024/25 (£4.15 million) but, across the whole of the Programme to date, was slightly above the September 2024 forecast (£3.95 million). This follows a Programme change request to transfer capital costs to fund a graphic processing unit (GPU) cluster to enhance processing capability, rather than rely on externally hosted IT services and platforms as planned originally in 2024/25.
Figure 2.1: Forecast and actual spend by Programme strand to end of FY 2024/25
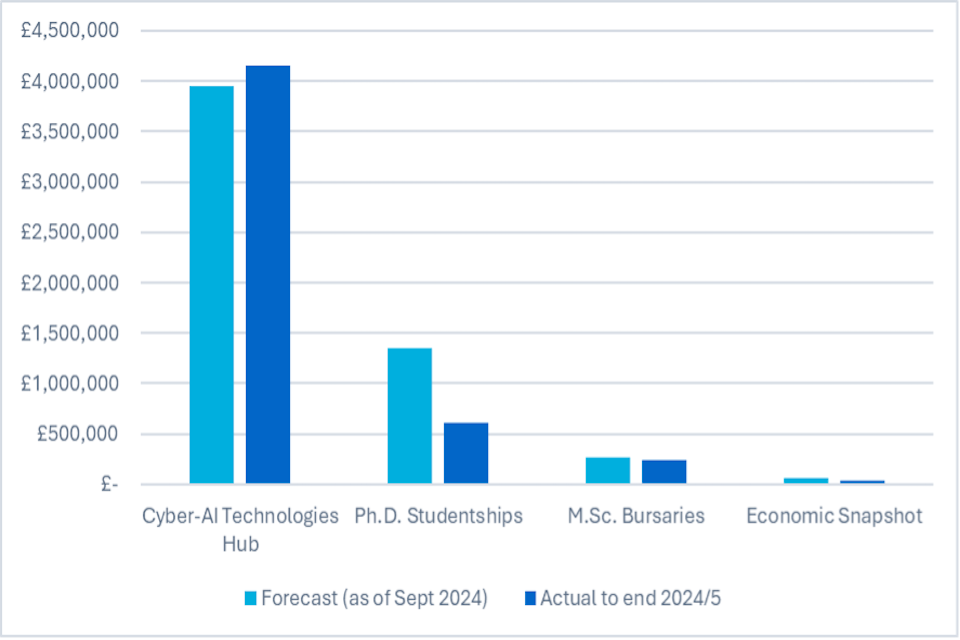
Source: Steer-ED analysis of Queen’s Monitoring Data, 2025
Spend on the PhD strand was lower at the end of FY 2024/25 than had been forecast in September 2024 (£605,000 vs. £1.34 million), resulting in overall spend in 2024/25 lower than forecast (£3.11 million vs. £3.69 million). This was due to a combination of two PhD withdrawals, and an underspend in student travel budget in that year.
The revised spend profile from July 2025 now shows anticipated higher spend in 2026/27, with the Technologies Hub the main driver of this – now forecast to spend £1.5 million in the final year of the Programme compared to a forecast of £1 million previously.
Figure 2.2: Spend by financial year for Programme overall, through to Programme end
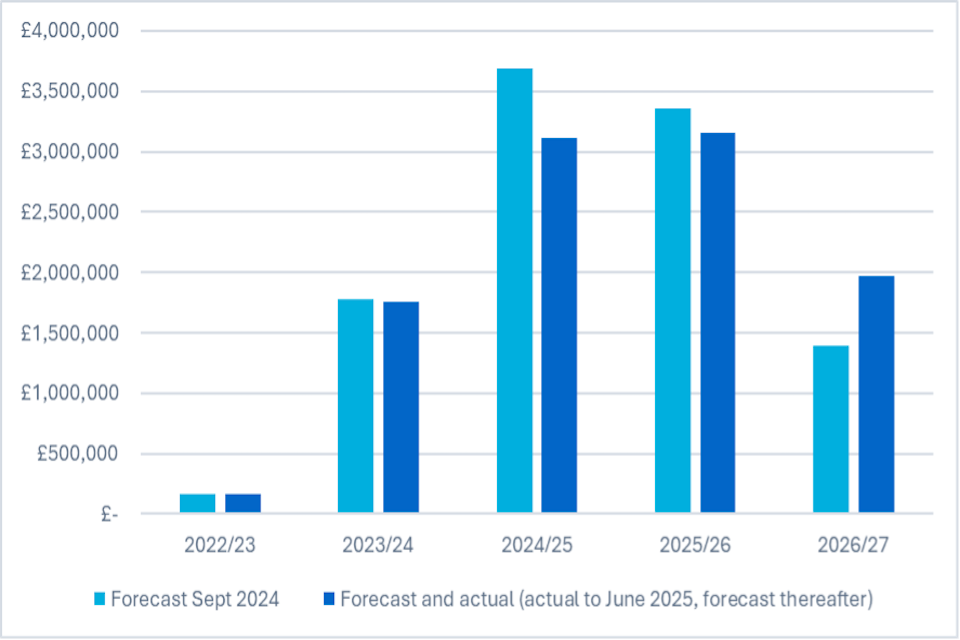
Source: Steer-ED analysis of Queen’s Monitoring Data, 2025
Progress by programme strand
The Cyber-AI Technologies Hub
The Technologies Hub initially included eight collaborative projects, bringing together businesses of different scales with academic principal investigators. The Programme experienced initial delays in mobilisation the reasons for which were covered in the previous evaluation report. These issues have now been resolved, with a delay legacy of around eight months, and the majority of projects now progressing well.
There has been some churn in the Programme strand since it began, with four of the original eight projects (Skurio, Cynalytica, Ampliphae, and Nvidia) having left for a variety of reasons. These include changes in personnel and strategic direction within participant firms led them to withdraw, reflecting the reality and pace of change across the business community and the knock-on impact of time delays.
Whilst these changes had implications for the Programme’s performance against the KPI relating to companies engaged, it reflects confidence in the participant companies and positive investment in NI’s cyber sector. Companies have already produced three minimal viable products through their engagement in the programme with more anticipated to ensure the MVP KPI remains on target.
To counterbalance this, Controlsoft joined the programme in March 2025. Another company is currently in the process of finalising agreement to join the Programme which will take the number of active projects back to six. The Cyber-AI Hub is actively exploring opportunities with alternative companies to increase the number of ongoing projects.
Figure 2.3 below depicts how companies have flowed through the Programme over time.
Figure 2.3: Timeline of project involvement in Technologies Hub project
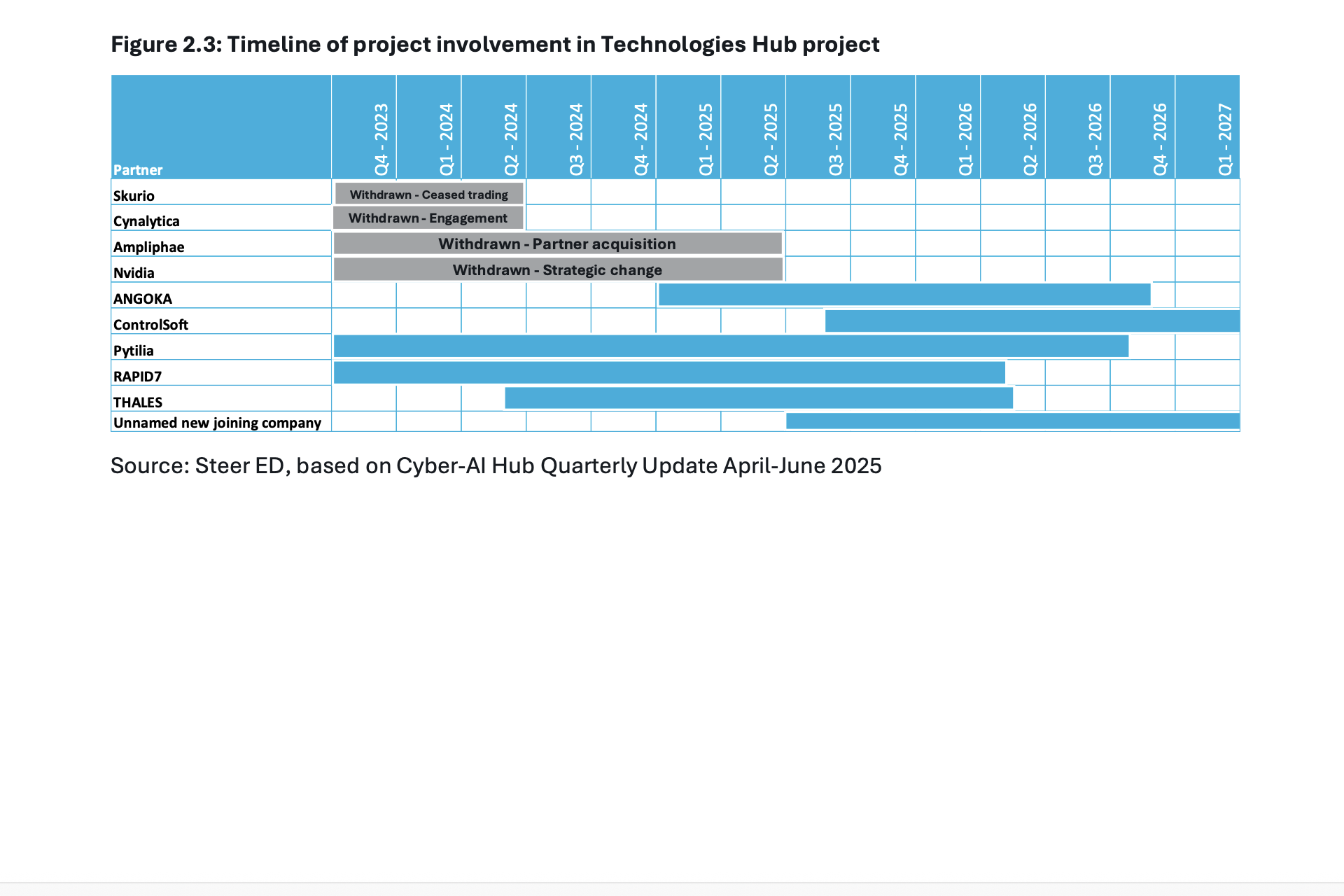
Source: Steer ED, based on Cyber-AI Hub Quarterly Update April-June 2025
A degree of churn is to be expected in Programmes such as this but, given the entry requirements for the Programme (particularly the requirement for a physical presence in NI), the pool of potential replacements is relatively small. Discussions have also been held with other prospective participant firms, though the window for projects to be developed, planned, and delivered is shortening.
Two companies involved in the Cyber-AI Hub have recently announced new job roles in Northern Ireland. Controlsoft announced 27 jobs in its Belfast engineering hub in July 2025; Following the acquisition of Ampliphae’s team and technology in May 2025, Arqit has invested in a new office location in Belfast and doubled the team size from 5 to 10 in that time. Arqit is currently hiring for an additional three roles and anticipates further hiring in 2026 for high-value technical roles in the cyber-security software and AI space. The company cites that Ampliphae’s involvement in the Cyber-AI Hub and the skills developed as a result were a significant factor in their decision to select Belfast as the location for their first development hub outside London.
The CSIT Doctoral Training Programme (DTP)
All 15 PhD students were recruited in 2023/24. Of these, 13 remain active within the strand, with two having withdrawn, one of whom chose to pursue a career in the local cyber security industry. Of those remaining in the strand, all are expected to complete by the end of March 2027.
Of the 15 PhD candidates, ten were locally domiciled prior to starting, three were domiciled in Vietnam, one in Bangladesh and one in Pakistan. All 15 of the recruited PhD candidates are male. Whilst the programme did not set objectives around diversity, a lack of gender diversity within the PhD cohort is evident. A more balanced cohort in the MSc programme offers signs of progress in this regard, which it is hoped and anticipated will feed through into more balance among PhD candidates in future as those pursuing MScs continue to progress in their studies.
To date, students in the DTP have produced a total of 26 academic contributions, including four articles/papers, twenty conference contributions, and one academic poster. More detail on these outputs is included in Chapter 4.
Through the promotion of the Cyber-AI Hub to CSIT’s existing industry partners, Qualcomm and Rolls Royce have each provided advice and guidance to students, as well as funding equivalent to two PhD top-up awards (which is used to benefit students across the cohort).
Industry placement opportunities have included three-month industry placements with Qualcomm’s hardware security team in Cork in October 2025, and the UK Telecoms Lab (UKTL) in Birmingham in September 2025. Another student joined the research team in Murcia University, Spain in Oct-Dec 2025 and another undertook a one-month placement with BT in Ipswich in Summer 2025.
Further potential placement opportunities in 2026 include Rapid7 (1), Qualcomm (1), Rolls Royce (2) in 2026.
The placements provide PhD researchers with valuable insights on industry challenges, input on their research, and new connections. It also helps to deepen CSIT’s engagement with industry partners by creating more connections and identifying opportunities for knowledge sharing and further collaboration.
The NICYBER2025 Masters Bursaries
To date, 32 students were enrolled on MSc courses across the 2023/24 and 2024/25 intakes. further seven have been recruited to begin study in September 2025, though demographic data on these additional students was not available at the time of this report.
Of those already in the Programme, eighteen students studying the MSc in Artificial Intelligence, twelve have achieved an MSc , three graduated with a PG Diploma and one with a PG Certificate. Two will resit in 25/26. Of the fourteen tudying the MSc in Applied Cyber Security, ten have achieved an MSc, two have graduated with a PG Diploma and one with a PG Certificate. One will resit in 25/26. Looking at the demographic breakdown of the MSc students, there are eight female students, of which three are studying the MSc in Applied Cyber Security, and the remaining studying the MSc in Artificial intelligence. The majority of MSc students (69%) have home addresses in Northern Ireland, 28% are from the United Kingdom, with one from Ukraine.
Figure 2.4: MSc intake by year (Full Time/Part Time status)
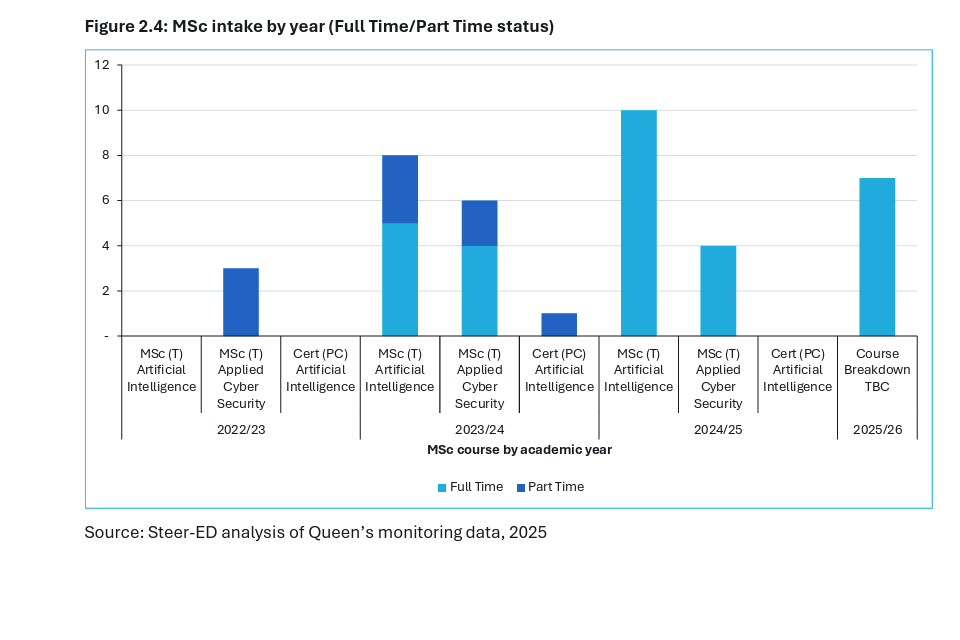
Source: Steer-ED analysis of Queen’s monitoring data, 2025
The Cyber-AI Hub team has engaged companies in the MSc programme, with Angoka, Ampliphae and Thales hosting student projects. Nvidia provided four intern opportunities for MSc students, including two Cyber-AI bursary students.
The NI Cyber Snapshot
The latest NI Cyber Snapshot[footnote 6] shows that cyber security continues to be one of the region’s economic success stories and Northern Ireland remains an international hotspot for activity in the sector with over 2,750 related roles generating more than £258 million direct GVA to the economy. However, the Snapshot also notes that the trajectory of growth has slowed considerably in recent years. This reflects global trends, with reductions in recruitment activity, inward investment, and growth capital identified in Northern Ireland.
Combined with macroeconomic conditions and technological shifts potentially impacting future growth trajectories, the Snapshot suggests that meeting Northern Ireland’s target of 5,000 jobs in cyber security by 2030 may be challenging. Given this, the snapshot suggests that increased focus should be placed upon wage and productivity levels and supporting the long-term sustainability and increasing seniority of roles within the sector.
Key messages
The target numbers of participants have now been recruited across the Technologies Hub, PhDs and MScs. The Technologies Hub experienced delays in mobilisation in its early phases due to issues related to subsidy control, but these were subsequently addressed and the Programme recruited to a peak of eight active projects. There has however been a relatively high degree of churn in this Programme, with four of the original eight private sector participants having withdrawn. Whilst two firms have successfully been recruited as replacements, and active recruitment is underway for others. It will be challenging for the Hub to achieve its target of eight completed projects within the remainder of the Programme.
The MSc and PhD programmes have also recruited effectively, albeit the MSc recruitment has been spread over an additional academic year. These strands have experienced a moderate amount of churn, which is to be expected in an initiative such as this. However, the tight recruitment criteria and the small number of eligible participants limits the ease with which any exits from the Programme can be replaced with participants of similar quality. The fact that numbers recruited aligned at their peak with the target for completions left no flexibility to account for drop outs and still meet targets. Whilst a degree of drop out is inevitable, this could have been mitigated by additional recruitment, or reflecting a degree of attrition in the target for completions.
The Programme has experienced underspend on some strands, but following mitigations such as bringing forward the capital purchase of the GPU cluster the Programme now expects to spend fully within the overall programme time frame. The spend profile has shifted somewhat to later years of the Programme, reflecting the above recruitment delays, and the Technologies Hub now accounts for a higher degree of spend than planned, with budget reallocated from the PhD programme following the two withdrawals.
3. Process reflections
Purpose
This chapter provides the findings on the process-related Research Questions addressed by this year’s evaluation research. It also provides an update on progress against the recommendations offered in last year’s evaluation monitoring report (‘Report 2’).
Findings on the research questions
P1 Is the programme being delivered as intended?
Overall, the Programme is broadly being delivered as intended in terms of the objectives and the scope of activities undertaken. As with any such programme, there have been challenges in delivery. In particular, we highlight the following:
- The financial profile has had to be amended to reduce the budgeted funding in earlier years and increase the funding in later years – reflecting the delays in getting the Programme underway;
- There has been considerable ‘churn’ in the companies engaged with the Technologies Hub strand. Of the eight companies involved at the outset of the Programme, four remain engaged. The delivery team has worked hard to secure replacement company partners for those who have left, but some of these have, in turn, had to withdraw. Reasons for companies ceasing their participation include: a company entering Administration (Skurio), a company being acquired (Ampliphae), and a project lead leaving the business (Nvidia). The Programme has currently five companies working on live Technologies Hub projects (Angoka, ControlSoft, Pytilia, Rapid7 and Thales), of which one (ControlSoft) joined only in 2025. Although discussions are ongoing with other potential partners, there remains a risk that the Programme will not achieve eight completed Technologies Hub projects in its current timescale. Those involved in the programme (both currently and historically) remain on track to produce the target number of minimum viable products (five);
- 15 PhDs were successfully recruited, but two PhD researchers have dropped out to date. As such, the Programme’s target of ‘at least 15 industry-conscious cyber security PhD graduates’ will not now be achieved. A degree of churn is expected in programmes such as this - the 2022 DCMS business case envisaged a cohort of 18 PhDs, and its benefits analysis assumed a drop-out rate of 10%-40% (i.e. 11 to 16 completions). Whilst aiming for 100% completion should be the objective, a more cautious/realistic outcomes target should be considered on future programmes;
- MSc recruitment has been slower than anticipated. Originally, two MSc cohorts were envisaged, each with 20 students. In practice, students have been recruited across four academic years of entry: 2022/23 to 2025/26; and
- As reported last year, the previous two annual NI Cyber Security Snapshot publications were pushed back from their original publication dates, although this has not compromised the value of these reports and enabled the reports to include the latest HESA statistics and align with similar UK reports.
P2 What has worked well, or less well, for whom and why?
Fieldwork consultees highlighted the following key areas as working well (see Chapter 4 of this report for more detail on early outcomes):
- In the two Technologies Hub projects used as case studies in this report, the close industry-academia collaboration was genuinely valued both by the companies and by the Queen’s academics. The Hub’s model is distinct from most R&D initiatives, involving much more integrated co-planning and co-working. This has led to substantial knowledge-transfer benefits for both sides;
- Having a critical mass of co-located PhD students in similar areas has been helpful in developing a community of interest. The additional stipend and the wraparound support for these students may be helping to minimise non-completions;
- The Programme’s networking events (including the events around each Quarterly Update on projects) are useful in building networks between companies, between companies and academics, and in giving PhD students visibility with companies and vice versa; and
- The NI Cyber Security Snapshot continues to be valued and well-regarded at NI and UK levels.
- Programme reporting has improved considerably over the last year, in terms of the quality and timeliness of financial tracking, forecasts, and claims.
The retention of companies engaging in the Technologies Hub projects was highlighted by consultees as a key challenge. As discussed above, this is largely due to factors beyond the control of the project teams. Consultees noted that there is a limited pool of companies in NI with the capability to engage in this level of R&D, making the recruitment of alternative partners challenging.
P3 Is the Programme meeting participants’ expectations of the Programme as advertised before participation?
On the basis of the Technologies Hub case studies undertaken for this report,[footnote 7] the Programme does appear to be meeting expectations, and both the companies and the academic leads are positive about the initiative. This is however based on the views of the two companies engaged in this phase of the evaluation and as such can not be considered a definitive finding. Research next year will seek feedback from all companies involved in the programme, including those to have withdrawn, to further inform this research question.
P4 Was the expected investment in time and resources for participating organisations manageable?
Again, for the two Technologies Hub case studies developed for this report, the required investment in time and resources has been broadly in line with expectations and manageable. Furthermore, this investment has been considered worthwhile, given the outcomes that are emerging – even though it is too early to say whether these R&D projects will directly lead to specific commercial products/services for the participating companies.
P5 Were there any unexpected or unintended issues in the delivery of the Programme?
Key issues highlighted by fieldwork consultees have been as follows:
- The churn in companies engaged in the Technologies Hub and the challenges of recruiting alternative partners in a relatively limited pool of NI-based companies with the capability to engage in R&D at that level, as discussed above;
- Notwithstanding good progress being achieved now, early challenges for the projects included developing an understanding of each others’ capabilities and needs, managing the tensions between industry and academia objectives and priorities, differing expectations on timescales for delivery/progress, and getting familiar with differing vocabularies;
- Initial challenges in programme reporting have now been addressed, enabled by additional financial team support within Queen’s. Innovate UK now consider the timeliness and quality of reporting as very strong compared to many similar programmes.
- Some churn in personnel within postdocs at Queen’s has reportedly been an issue for some projects, entailing the need to bring new colleagues up to speed. Retention of highly-skilled university staff is particularly challenging in areas such as cyber and AI, given that the higher salaries available in industry are a considerable draw, so this churn issue is not surprising; and
- In one case, the consultee commented that responsibility for bearing the required cloud compute costs had been ambiguous in the initial project budget.
P6 How could delivery of the Programme be improved?
The general consensus amongst consultees was that the Programme had now got into a good ‘rhythm’ and was working well. Few specific opportunities for improving the Programme in its remaining 18 months were identified.
However, there was a consistent message from several consultees that the Programme seems to be a ‘well-kept secret’ with limited direct visibility beyond the immediate participants, despite an evident increase in engagement, events and networking opportunities. It was acknowledged that, in the case of the Technologies Hub, this was a function of the type of activities involved: relatively long and high-risk R&D projects, without a guarantee of leading to commercial products/services, and with commercial confidentiality considerations. Some suggestions on how awareness of the Programme’s activities could usefully be further enhanced are provided in Chapter 5 of this report.
P7 How have external factors influenced the delivery and functioning of the Programme?
Since the genesis of the Programme in 2021, external events have only served to strengthen the importance of AI and cyber and the intersections between them, and some consultees noted that the Programme was highly prescient in anticipating this. Sparked by the launch of ChatGPT in late 2022, government and industry interest has boomed in how AI can be used to enhance productivity and transform organisations’ processes and business models. The recent spate of high profile cyber breaches in the UK (e.g. Co-op, Marks & Spencer, Jaguar Land Rover) have emphasised how crippling such events can be, and have kept cyber security towards the top of the agendas of private and public sector organisations. The problem is however broader than the cases which make the headlines, with as many as four in ten businesses reporting some form of cyber security breach in the last 12 months.[footnote 8] The emerging use of AI is now a key aspect of cyber security approaches (although it is also being used by bad actors in planning and executing cyber attacks).
As discussed above, external factors related to specific companies have provided some headwinds for the Technologies Hub: with changes in individual companies’ solvency, ownership, key personnel or strategy leading to churn in the participating firms.
The advent of Generative AI – and, in particular, its use by software companies for coding – has, according to anecdotal evidence from consultees in this study, suppressed demand for entry-level recruits. This is likely to have made the job market more challenging for graduates from the Programme’s MSc courses than was the case when the Programme was first conceived. This is further evidenced by recent analysis of the UK’s cybersecurity labour market for DSIT.[footnote 9]
Other publicly-funded initiatives have emerged since the Programme was first introduced, which have complementary or closely related objectives, and which offer opportunities for collaboration/synergies with the Cyber-AI Hub programme. In particular:
- LASR (Laboratory for AI Security Research) is a UK public-private partnership dedicated to mitigating AI security risks for UK national security and economic prosperity, in which Queen’s is a key delivery partner. It currently has £8.2 million of public funding;
- AICC (AI Collaboration Centre) is £16.3 million initiative involving Ulster University and Queen’s, promoting AI awareness and adoption among businesses in Northern Ireland. It includes funding for 195 MSc bursaries for AI-related courses at UU and Queen’s; and
- The UK Government’s £187 million TechFirst programme includes funding for 100 Research MSc places in key tech sectors, and 100 elite AI scholarships, and an extra £10,000 in funding to 500 domestic PhD students in tech.
P8 Was the Programme design and activity set appropriately in delivering the anticipated outcomes?
The broad consensus amongst consultees was that the Programme’s design was – and remains - appropriate in addressing its intended outcomes: the talent pipeline remains critical, and appropriate funding for MScs and PhDs is important for this; and supporting collaborative industry-academia research related to the use of AI in cyber security, and the security of AI models, could be important in helping to retain/safeguard and expand Foreign Direct Investment companies’ operations in NI, and in boosting the growth prospects for indigenous NI cyber companies.
However, stakeholders perceived that the governmental target of 5,000 cyber professional jobs in Northern Ireland by 2030 looks in some doubt given the recent slower growth in the sector. Furthermore, the Programme’s target contribution of 150 additional cyber security jobs created or safeguarded now appears to be optimistic on the basis of evidence collected so far for this evaluation.
P9 Cyber-AI Technologies Hub: Was there common understanding amongst participants on the objectives and intended outcomes of the Cyber-AI Technologies Hub?
Based on the two Technologies Hub case studies undertaken for this report, there was a common understanding of the projects’ objectives and intended outcomes, shared by the industry and academic leads. Interviewed separately, the parties gave similar unprompted responses to the anticipated benefits for both Queen’s and the participating companies.
P10 Cyber-AI Technologies Hub: How did projects work collaboratively? Was there sufficient engagement from both industry and academia?
For the two case studies, the collaboration was, and is, working well, with sufficient engagement on both sides. Joint planning sessions every three weeks were highlighted as being particularly important in ensuring effective communication and collaboration between the industry and university partners, and crucially making sure that expectations (from both business and academics perspectives) were well aligned.
However, the churn experienced by the Technologies Hub on other projects suggests that industry engagement and commitment may not – in some cases - have been sufficiently deep and strategic to survive disruptions such as delays in finalising contracts, a project lead leaving the company or a change of ownership. We will be conducting research with companies that withdrew from the Programme for next year’s evaluation monitoring report to provide learning on this aspect.
Progress on previous recommendations
Last year’s evaluation monitoring report included five recommendations. The table below summarises progress on each of these.
Table 3.1: Progress against previous recommendations
| # | Recommendation | Progress |
|---|---|---|
| 1 | Report financial data (budget, actual and forecast) quarterly by programme component | • Reporting has substantially improved over the last year, and the financial reports now include a breakdown by programme component. |
| 2 | Improve the timing of and provide greater detail in the NI Cyber Security Snapshot including in relation to skills supply and recruitment flows, and sector changes over time. | • A summary 2024 NI Cyber Security Snapshot was published in September 2024. This included a statement that ‘A full NI Cyber Security Snapshot (2024) will be published in late-2024’. The full version was completed in November 2024. The Snapshot was made available on the CSIT website. • Discussions are currently ongoing between Queen’s and Perspective Economics re the scope of the 2025 Snapshot report, which is due to be available in December 2025, and will be published to CSIT’s website, alongside the 2024 version. |
| 3 | Establish clear milestones, deliverables and forecast expenditure for the Technologies Hub projects to report against on a quarterly basis | • Quarterly update slides for each project now include Gantt charts showing percentage progress against each task, and a table summarising the status of each deliverable. These slide packs are informative and helpfully transparent. |
| 4 | Enhance collaboration between the Technologies Hub projects. | • Feedback from consultees for this year’s reports suggests that the Programme’s regular networking events have increased the visibility across the Hub’s projects, and provided additional opportunities to build links between participating companies (as well as between the companies, academics and PhD students). |
| 5 | Document and apply learning on subsidy control | • We understand that subsidy control is now a prominent consideration in DSIT’s project development/appraisal. • Whilst the issues experienced at the programme’s outset were specific to this programme and its timing coinciding with legislative changes, Innovate UK have disseminated learning from this experience. New processes have since been introduced which would have been a suitable mechanism for this programme and should minimise the risk of similar issues in future. |
Source: Steer-ED, 2025
Key messages
Since the genesis of the Programme in 2021, external events have only served to strengthen the importance of AI and cyber and the intersections between them, and some consultees noted that the Programme was highly prescient in anticipating this.
Overall, the Programme is broadly being delivered as intended in terms of the objectives and the scope of activities undertaken.
The MSc and PhD strands are on course to deliver substantive numbers of skilled graduates. However, the PhD strand will not now achieve 15 PhD graduates, given the two withdrawals to date.
In the two Technologies Hub projects used as case studies in this report, the close industry-academia collaboration was genuinely valued both by the companies and by the Queen’s academics. The Hub’s model is distinct from most R&D initiatives, involving much more integrated co-planning and co-working. This has led to substantial knowledge-transfer benefits for both sides.
The churn in participants in the Hub presents a challenge, but this is being effectively managed and mitigated by the project team.
4. Evidence of early outcomes
Purpose
In the context of the preceding section on Process Findings, this chapter provides early and initial perspectives on the outcomes which the Programme is starting to give rise to. These perspectives are built on (i) data analyses of the PhD and MSc strands, (ii) study consultee feedback on emerging outcomes and early impacts across the Programme, and (iii) case studies undertaken with two firms participating in the Technologies Hub strand.
The core purpose of this report as a whole is to provide interim evidence and thinking on the developing processes supporting the Programme’s delivery. From this perspective, the report acts as an extension of Report 2, produced in Autumn 2024, which provided the initial process evaluation assessment.
But as well as being an extension to last year’s process work, this report starts to provide evidence and early thinking on the Programme’s developing outcomes which, together with achievement of the objectives as at Figure 1.1, will be the prime focus of next year’s ‘Report: developing outcomes and early impact evaluation’. In this sense, this report starts to provide the bridge between the process and output/impact objectives which are at the heart of the overall evaluation.
The evidence on these developing outcomes is drawn from three sources:
- Analysis of the outcomes starting to flow from the PhD and MSc streams, where the data sets are now well populated and developed;
- A review of the study consultees’ qualitative perspectives on the outcomes which are starting to flow from the Programme; and
- A pair of case studies of Cyber AI Technologies Hub projects, undertaken with participant firms and Queens’s Principal Investigators.
Data analysis of the outcomes flowing from the PhD and MSc streams
PhD publications
13 of the 15 PhD candidates remain active in the Programme and have been involved in producing publications, primarily in the form of conference contributions, but also journal articles, and papers. Table 4.1 presents details of the 25 publications produced to date, along with the number of citations and downloads of each as of 8th October 2025.
Table 4.1: Summary of publications involving Cyber-AI Hub PhD students (2023-2025)
| Title | Publication date | Category | Location | Publisher | Citations | Downloads |
|---|---|---|---|---|---|---|
| Investigation of communication overhead of SoC lookaside accelerators | November 2025 | Conference Contribution | United States | NA | 4 | 147 |
| An investigation of machine learning algorithms for high-bandwidth SQL injection detection utilising BlueField-3 DPU technology | November 2025 | Conference Contribution | United States | NA | 3 | 0 |
| Deep learning enhanced side channel analysis on CRYSTALS-Kyber | May 2024 | Conference Contribution | United States | Institute of Electrical and Electronics Engineers Inc. | 3 | 581 |
| Reconstructing suspended sediment concentrations in the Mekong River Basin via semi-supervised-based deep neural networks | December 2024 | Article | NA | Science of the Total Environment | 2 | 0 |
| Quasi-omnidirectional millimetre wave 5G handset antenna | May 2023 | Conference Contribution | Italy | NA | 2 | 36 |
| Network intrusion response using deep reinforcement learning in an aircraft IT-OT scenario | July 2024 | Conference Contribution | Austria | NA | 1 | 115 |
| LoRa radio frequency fingerprinting identification using a hybrid quantum-classical neural network | November 2024 | Conference Contribution | United States | Institute of Electrical and Electronics Engineers Inc. | 1 | 0 |
| Detection of UE metric data poisoning in O-RAN: automated risk analysis and resilience | August 2025 | Article | NA | IEEE Communications Standards Magazine | 1 | 0 |
| Effect of left-handed grip on coverage of quasi-omnidirectional millimetre wave 5G handset antenna | May 2023 | Conference Contribution | Italy | Institute of Electrical and Electronics Engineers Inc. | 1 | 70 |
| Understanding the security implications in O-RAN with abusive adversaries | July 2024 | Conference Contribution | Vietnam | NA | 0 | 5 |
| A wolf in sheep’s clothing: evading robust aggregation in federated learning through in-distribution attacks | March 2025 | Conference Contribution | Ireland | Institute of Electrical and Electronics Engineers Inc. | 0 | 10 |
| Preserving spatial-temporal relationship with adaptive node sampling in hierarchical dynamic graph transformers | January 2025 | Conference Contribution | Vietnam | NA | 0 | 0 |
| DeepPUFSCA: deep learning for physical unclonable function attack based on side channel analysis support | February 2025 | Conference Contribution | United States | IEEE | 0 | 0 |
| PEVuln: a benchmark dataset for using machine learning to detect vulnerabilities in PE malware | February 2025 | Conference Contribution | United States | CEUR-WS | 0 | 195 |
| InteDisUX: interpretation-guided discriminative user-centric explanation for time series | April 2025 | Conference Contribution | United States | AAAI Press | 0 | 26 |
| Microarchitecture design and benchmarking of custom SHA-3 instruction for RISC-V | August 2025 | Conference Contribution | Greece | NA | 0 | 0 |
| Cascade error correction attack; exploiting implicit and side channel information leakage | May 2025 | Conference Contribution | Japan | NA | 0 | 11 |
| Epidemic Oracle: an approach to boost security and performance of delay tolerant networks | May 2025 | Conference Contribution | Italy | IEEE | 0 | 0 |
| Design and prototyping of custom SHA-3 instruction for CVA6 RISC-V Core | September 2025 | Conference Contribution | U.A.E. | NA | 0 | 0 |
| Performance impact of caches, interrupt strategies and communication on SoC lookaside acceleration | September 2025 | Conference Contribution | U.A.E. | NA | 0 | 0 |
| DEV-PIM: dynamic execution validation with processing-in-memory | July 2023 | Conference Contribution | Italy | NA | 0 | 0 |
| WaveletMixer: a multi-resolution wavelets based MLP-mixer for multivariate long-term time series forecasting | December 2024 | Paper | United States | NA | 0 | 0 |
| QL-PGD: An efficient defense against membership inference attack | July 2025 | Article | NA | Journal of Information Security and Applications | 0 | 0 |
| On the limitations of fuzzy hashing for malware similarity: an analysis of vulnerable code detection in malware | October 2025 | Conference Contribution | China | IEEE | 0 | 0 |
| SOC Accelerator Communication Overhead: Impact of Cache, Data Size and Communication Handling | December 2024 | Poster | NA | NA | NA | NA |
| Evaluation of autonomous intrusion response agents in adversarial and normal scenarios | October 2025 | Conference contribution | France | Springer Cham | 0 | 2 |
| Defending AI-Enabled Radio Access Networks: Detection, Modelling and Resilience | October 2025 | Other contribution to conference | Ireland | TBC | 0 | 0 |
Source: Queens University Belfast Publications (https://pure.qub.ac.uk/en/publications/), as at 30 September 2025
Whilst many have been published in 2024 and 2025 and have limited citations, there are a small number of recent publications that have generated a large number of downloads which could be indicative of their value and usefulness to the academic community. More detailed analysis in the future impact evaluation will explore this more fully.
MSc achievements and destinations
As of July 2025, analysis of Cohort one’s outcomes indicates that 12 students successfully passed, representing 67% of the group. Among those to have graduated, five have graduated with an MSc in Applied Cyber Security, five with an MSc in Artificial Intelligence, and two have completed alternative post graduate qualifications.
Among those who are yet to graduate, one has requested to pursue a postgraduate diploma, and five returned to take additional credits during the 2024/25 academic year.
Of the twelve to have graduated so far, a search of LinkedIn was undertaken to assess destinations for the graduate’s post-completion. It should be noted that the LinkedIn search was conducted in October 2025, and as such, the information reflects employment status at that point in time. Furthermore, reliance on social media profiles introduces limitations on the validity of these results. Not all graduates will maintain up-to-date or accurate representations of their professional status online. Some individuals may not use LinkedIn actively, while others may have privacy settings that restrict visibility, potentially leading to incomplete or misleading conclusions. Of the nine with LinkedIn profiles:
- Two are with new employers (both MSc Applied Cyber Security graduates)
- Two remain employed with the same organisation as they were with at the start of their course. However, conclusions that can be drawn from this are limited due to the potential for inactivity on their LinkedIn account’s or an out of date employment status.
- Three have progressed into further study (including two now undertaking PhDs in Artificial Intelligence at Queen’s)
- Two had no current employer listed.
Review of the study consultees’ qualitative perspectives on the outcomes
As part of the field work consultations (n=16) undertaken for this report, interviewees were probed for their views and perspectives on the early outcomes that were becoming apparent from the Programme’s four strands.
Overall programme awareness and profile
Whilst consultees were generally well aware of what the Programme is seeking to achieve in overall terms, there was little detailed understanding of the outcomes expected, and flowing, from the initiative’s four strands. The reasons here were mixed. These included a lack of detailed understanding or awareness of what each strand was expected to generate. There was also limited alignment between the consultee’s role and the specific activities being delivered by the Programme strands. For those whose activities are aligned with the Programme, there was recognition that the initiative, following initial delays, is only now beginning to build its ‘equilibrium momentum’.
Notwithstanding this, a number of themes were largely consistent:
- Of all four of Programme components, the Snapshot was the most commonly ‘recognised’. As a published and circulated resource, frequently being drawn on by those with policy and/or sector interests, the Snapshot is seen as an important and informative resource, playing an influential role in raising the profile of Northern Ireland’s cyber AI sector, markets, and technologies. This was reported on largely consistently as a valuable existing outcome for the Programme;
- On the PhD and MSc strands, these were seen as important channels by which Northern Ireland’s skills and talent pool could be built to help underpin the cyber AI sector. A small number of consultees commented on the greater importance that might be given to PhDs as cyber AI technologies became more sophisticated and demanding, and a couple of respondents commented on the constrained job market for MSc students as Generative AI becomes yet more sophisticated. There was essentially no comment on the employment outcomes or salary-earning additionality of the PhD and MSc strands at this point, essentially because consultees were not close enough to the detailed working of these strands of the Programme;
- The Technologies Hub (and its associated projects) was seen commonly as the ‘core essence’ of the Programme, linking firms with Northern Ireland presence to specialist academics at Queen’s. However, given the commercial and security sensitivities involved in the subject matter, it is difficult to promote/market activity taking place in the Programme. As such, whilst there was a broad name recognition of the firms undertaking Technologies Hub projects, there was little substantive understanding what these projects comprise, and what they might give rise to in terms of new products, technologies, and/or employment opportunities. Importantly, no consultee commented explicitly on the employment creating achievements of Technologies Hub projects, again not a surprising finding if the detailed nature of projects and their markets is not broadcast. This does flag an important tension for the Programme - a set of smart and in many cases market-leading R&D projects, but because of commerciality sensitivity, there is little scope for this activity to be communicated more fully to Northern Ireland’s business and sector communities. Work is warranted here to think through how this commercial sensitivity versus programme marketing conundrum might be addressed going forward.
On a wider contextual point, there was an evident concern from a number of consultees as to whether the New Decade New Approach commitment of 5,000 new cyber jobs in Northern Ireland by 2030 was going to be achieved. It is worth remembering that 150 of these jobs are due to be generated by the Programme; the Programme’s Delivery team will want to review the achievability of this target carefully, in the context at this stage of no measurable direct employment creation from Hub projects. Phases 4 and 5 of this evaluation will include more specific focus on impact, and will seek to answer this question directly via engagement with participating businesses.
Wider strategic added value outcomes
[1]Strategic added value (SAV) represents those softer, qualitative outcomes and impacts delivered by publicly funded intervention, complementing those quantified direct and indirect effects. In the context of the Cyber-AI Programme, SAV takes in the following:
- Articulating and communicating Northern Ireland’s cyber AI development needs, opportunities and solutions to partners and stakeholders in NI and elsewhere;
- Influencing partners so that they commit to shared strategic objectives and behave and align their funds accordingly;
- Leveraging wider resources and support from partners, including central government departments and the private sector, by providing appropriate incentives;
- Using its organisational capacity, knowledge and expertise to improve information exchange, knowledge transfer and co-ordination of the design and delivery of interventions between partners; and
- Setting up mechanisms and incentives for more effective and deliberative engagement of stakeholders in the design and delivery of regional and sub-regional priorities and programmes.
The Programme’s SAV will be more fully probed and characterised in evaluation Reports 4 and 5, due in 2026 and 2027 respectively. But at this interim stage, the following aspect of SAV are noteworthy:
- The thinking which Queen’s had undertaken in developing the Programme’s concept was viewed as ‘pioneering and influential’ in shaping the establishment of the UK’s Laboratory for AI security Research (LASR), which is being delivered as part of the Government’s commitment to position the UK as a global leader in AI security and governance;
- A second consultee noted the Programme’s role in embedding R&D within Northern Ireland firms, also referring to the Programme’s role in influencing national cyber AI strategy (e.g. through its membership of LASR);
- A third consultee referred to the role of the Programme’s Technologies Hub strand in enabling technology development and, with the Snapshot, helping to define and characterise the cyber AI ecosystem in Northern Ireland;
- A further consultee commented on the valuable role the Programme was playing in building awareness of AI in cyber settings at large in Northern Ireland; and
- A final consultee commented on the role of the Programme as a ‘highly regarded’ model of academic-industry synergy and collaboration.
Realising the benefits . . .
Recognising that the Programme is now at the end of its third year, these are still relatively early days for substantive Programme outcomes and impacts to become apparent. This recognised, study consultees were probed on how the realisation of benefits might be progressed. Here, the key suggestions included:
- Ensuring optimum linkages between the Programme and the newly launched Artificial Intelligence Collaboration Centre (AICC), with another consultee commenting on the role of this operational link in translating leading-edge research into useful tools for smaller firms in NI;
- Testing the scope for the Programme to build links with GCHQ (both at Cheltenham and in Manchester) and with the Cyber Corridor being developed between Manchester and Preston; and
- Developing the Programme’s links with Momentum 1.0, the ACE Network, Cyber ASAP and Cyber Runway
. . . and optimising those Benefits
Consultees were also asked what the Programme might usefully do to amplify its benefits. Here, suggestions for improvement included:
- Queen’s providing stronger Programme ‘marketing and storytelling’ in the round to raise the profile of the initiative, and to diffuse and embed awareness more widely (this recognising existing outreach efforts, such as CSIT’s Trustworthy AI Chronicles podcast; inclusion of PhD researchers in the monthly NI Cyber Breakfast Club events attended by c. 40-60 individuals from the cyber industry; and promotion of Cyber-AI Hub and industry partners during CSIT Summit Oct 2024, NICON Silicon Valley May 2025, CSIT Open Day Sept 2025 and Big Data Belfast Oct 2025);
- Better promoting the company-level outcomes and impacts arising from Technologies Hub projects to help seed and encourage further firm-academic collaboration;
- Being alert to the needs of Northern Ireland’s SMEs with cyber AI interests and challenges, building on the good work undertaken by the Programme with larger firms.
Early thoughts on programme succession
As a closing topic, consultees were probed about Programme succession. Here, whilst DSIT currently has no plan for funding continuation, two consultees advocated firmly for a five-year extension for the Programme, combined with a UK, and potential international, rollout for the Programme. Another consultee encouraged early planning with a successor funder, possibly via IUK or LASR. A closing consultation also highlighted the reality that market forces alone were unlikely to deliver a long-term R&D solution in the cyber AI space, thus creating a potential rationale for Programme continuation.
Outcomes evidence emerging from this report’s two case studies
Two case studies were undertaken for this report, designed to start to tease-out the range and richness of outcomes and early impacts flowing from Cyber Technologies Hub projects. The first case study was with Pytilia, a Belfast-based firm employing about 50 people, the second with Rapid7 a larger business employing 500 people in Belfast, and headquartered in Boston.[footnote 10]
Case study summaries of the projects and the benefits flowing for firms and Queen’s are summarised in the panels below. Both case studies were guided by the research questions defined for the Programme’s impact evaluation set out in February 2024’s Evaluation Plan, but the interim nature of each case studies’ projects meant that these questions could only be applied lightly. Deeper and more forensic assessment of Technologies Hub project outcomes, impacts, and value for money will be addressed in Reports 4 and 5, in 2026 and 2027 respectively.
These caveats noted, in terms of early gross outcomes and impacts, there are common themes across both examples:
- Each case study highlights the potential for commercial benefits, although for both examples this is a good way downstream, so uncertainty at this point is high;
- Both examples point to helpful learning for both company and academic company teams and staff, with efficient and effective ways of working now established and being applied. For one of the examples, the maturity of the working relationship has meant it has been possible to make substantive ‘in flight’ changes to project direction and focus;
- There is potential scope for academic publications arising from the projects, although further work is needed from the academic side and so, again, there is some uncertainty; and
- The association and collaboration with the Cyber-AI Technologies Hub, and CSIT more generally, is viewed as reputationally and materially important to both participant firms as they develop new business opportunities.
Case Study 1 – Pytilia
Corporate IT networks and systems face a daunting volume of potential security vulnerabilities. The Common Vulnerabilities and Exposures (CVE) database currently lists over 290,000 publicly disclosed cyber security vulnerabilities across thousands of different products. Many companies are overwhelmed by the challenge of determining which security threats are most serious in their specific business context and how best to allocate resources.
Pytilia’s ‘Context Aware Vulnerability Detection and Mitigation’ project with Queen’s under the Cyber-AI Technologies Hub programme aims to develop an automated solution for this challenge, powered by AI: saving time, and providing a more comprehensive and systematic approach to addressing the risks posed by cyber security vulnerabilities. The project kicked off in November 2023, and is scheduled to complete by March 2026.
The idea is to develop a dynamic threat assessment engine, which will:
- Characterise the organisation’s tech stack, including the various current products and versions and the criticality of each asset within the organisation’s business processes;
- Obtain information on known vulnerabilities from various external sources, including information on the tactics and techniques used by threat actors and the extent to which each vulnerability has already been weaponised;
- Determine the applicability of each vulnerability to the organisation’s specific tech stack;
- Calculate a risk assessment score, taking into account the criticality of affected products, and the exploitability of the vulnerabilities;
- Analyse groupings of known security vulnerabilities, to help predict new vulnerabilities that may arise for the organisation in the future; and
- Provide multiple ways to allow users to determine current priorities for the organisation and view supporting context, including a dashboard and a prompt interface, which will support natural language queries
Benefits for Pytilia
For Pytilia, this R&D project could potentially result in a new product offering, differentiated from solutions available from larger players, which helps to address a major issue for many businesses’ cyber security teams. If so, this would lead to enhanced turnover, profit and employment growth within this Belfast-based company.
However, a substantial benefit that is already being realised is around skills and knowledge transfer: the direct engagement between Pytilia engineers and the academics at Queen’s has had a material impact in building up skills within Pytilia that are applicable to other commercial opportunities: for example on Retrieval-Augmented Generation (RAG) and GraphRAG pipelines using LLMs.
The company also values the relationships being built up with Queen’s staff, both through this project and through other initiatives: connections which are already proving valuable beyond this specific project. The networking events organised by the Programme have also helped Pytilia develop stronger relationships with other companies involved in Technologies Hub projects, complementing other networking opportunities such as NI cyber events.
More widely, the project brings benefits for Pytilia in terms of market positioning: it is a tangible example of Pytilia’s engagement with universities, which enables the company to stay at the forefront of research and to translate leading-edge academic insights into real-world innovative solutions for clients.
Benefits for Queen’s
For Queen’s, a key benefit is that this project provides a real-world use case for translation of academic research into a potential commercial offering. This provides the academics with insights into the practicalities of taking a concept through to implementation, as well as exposure to software engineering best practice (for example around Continuous Integration and Continuous Deployment). It also offers a useful reality-check on some of the assumptions underpinning the academics’ work, and is helping to inform their future research direction.
Furthermore, the project is having some impact on teaching at Queen’s. For example, it has led to the development of a new mini module on the pipeline for deploying RAG models, for inclusion in the MSc course in Artificial Intelligence (which is led by one of the project’s Principal Investigators at Queen’s). Pytilia also provided a research project on anomaly detection which was taken up by one of the students on the MSc course in AI.
As is the case for Pytilia, the academics at Queen’s value the industry-academia relationships being developed through the project. These can only help improve the alignment between university research and industry needs, and could lead to future collaboration opportunities.
Although the project has not led to any scholarly publications as yet, there is a reasonable chance that aspects around vulnerability prediction will warrant publication. If the project does bring about a new product offering, that could provide a valuable impact case study for inclusion in Queens’s submission under the Research Excellence Framework assessments.
Issues encountered
Although the project kicked off in November 2023, there was a substantial delay in finalising the contract as the programme worked to resolve subsidy control issues and some negotiation regarding intellectual property. The contract was only signed in August 2024. This made it difficult to share intellectual property or have a common codebase in the early stages.
Initially, there was somewhat limited visibility within Pytilia of Queen’s progress and planning on the project, but this was resolved by moving to joint planning sessions between Pytilia and QUB every three weeks, which have played a big part in making the collaboration work. These are in-depth technical sessions, reviewing what’s happened since the last sprint, and getting feedback from the Queen’s Principal Investigators and from Pytilia.
Other issues included: the need to establish a common understanding and vocabulary in the early stages of the project, such that both sides were clear on the needs and capabilities of the other party; a lack of clarity in the initial budgeting as to which party would bear the compute costs; and some churn in personnel within the Queen’s team. However, such issues have been managed effectively through a transparent and collaborative approach.
Summary
Overall, both Pytilia and the academic leads at Queen’s are very positive about the project, which has found a productive ‘rhythm’ as the work has gone on, and is generating benefits for both sides from the close industry-academia collaboration.
Pytilia has greatly benefited from the academic and engineering collaboration at the core of the Cyber AI Technologies Hub, enabling knowledge sharing and skills development essential to our future. Our project within the Technologies Hub provides an ideal platform to advance Pytilia’s commitment to R&D, continuous innovation, and the wider cyber security ecosystem. We look forward to building on our partnership with Queen’s University into the future.
— Darren Borland, Cyber AI Technologies Hub Project Lead, Pytilia
Case Study 2 - RAPID7
Cybersecurity in the cloud is a growing concern for all organisations. As they progressively migrate their operations to, and distribute their operating environments on, cloud platforms, the complexity of managing sensitive data, user access, and threat detection has grown. Increasingly, businesses and public policy makers are thinking through how emerging technologies like Artificial Intelligence (AI) can help address these risks.
Rapid7’s collaboration with Queen’s under the Cyber-AI Technologies Hub Programme is focused on applying AI to these challenges, with the aim of improving detection, triage, and response capabilities in cloud-based systems.
Project Overview
The project comprises two workstreams:
- Work Package 1 (WP1), launched in May 2024 and completed in early 2025, explored the use of AI to identify sensitive data in public cloud services, such as AWS S3 buckets. Although the original hypothesis was not fully proven, the project yielded a valuable technological side outcome around anomaly detection. This outcome is undergoing internal evaluation in Rapid7, prior to consideration for integration into Rapid7’s broader cloud response offerings.
- Work Package 2 (WP2) was scoped initially to address Cloud Identity Entitlement Management (CIEM), but was cancelled in late CY2024 following a shift in Rapid7’s wider strategic thinking. A revised WP2 was then scoped, focused on developing an AI-powered alert triage model to support Rapid7’s Managed Detection and Response (MDR) services. This new workstream is expected to complete by February 2026.
Benefits for Rapid7
Rapid7 sees significant potential commercial value from the anomaly detection technology flowing from WP1, which could rival existing solutions such as Amazon GuardDuty. While not a direct product launch, the IP generated from WP1 has the potential to enhance Rapid7’s offerings and contribute to future revenue streams.
The project has also supported internal skills and knowledge development, with Rapid7 engineers gaining deeper insights into AI applications for cloud security. The project has helped the company secure new business, including a multimillion-pound deal with a UK customer, where Rapid7’s investment in AI and its partnership with Queen’s were key differentiators.
More broadly, the project has further strengthened academic relationships between Rapid7 leads and Queen’s researchers. The company is exploring further opportunities for MSc-level engagement, and hosting of PhD placements.
Benefits for Queen’s
For Queen’s, the project has provided a real-world use case for applying academic research to enterprise-scale cloud security challenges. WP1 offered valuable experiential learning in cloud environments and helped the academic team better understand the needs of large-scale businesses.
The revised WP2 project continues to support Queen’s’ research agenda, particularly in threat detection and AI-driven alerting.
The project has also facilitated knowledge transfer, with engineers sharing insights across Queen’s’ Post Doctoral group, and has helped build further the strategic partnership between Queen’s and Rapid7 which could lead to future joint initiatives
Issues encountered
Several challenges were encountered during the project:
- Shifts in Rapid7’s strategic thinking led to the pivot from the original WP2, requiring flexibility and innovative thinking from both sides as a new WP2 workstream was developed;
- Differences in the working styles of business and academia, particularly around the urgency of timelines within the Cyber-AI Hub project and business priorities . Progressively, these were addressed by careful project management and regular communication;
- Remote working dynamics posed some logistical challenges, with Queen’s tending to favour face-to-face collaboration and Rapid7 operating a more distributed way of working (especially around collaborative communication platforms such as Teams) and Slack;
- Subsidy control issues created delays and uncertainty early in the project, though these were ultimately resolved with support from Programme staff.
- Despite these issues, both parties are seeking to collaborate effectively, with the revised WP2 project set to benefit from the co-working style established during WP1.
Summary
Overall, Rapid7 and Queen’s are highly positive about their collaboration under the Cyber-AI Technologies Hub. The project has delivered tangible technical outcomes, further strengthened relationships, and has started the process of alignment between academic research and enterprise, crucial to deliver synergy and value add.
Our partnership with CSIT through the Cyber AI Technologies Hub has delivered real, tangible benefits, advancing Rapid7’s capabilities in using AI for securing our customers’ attack surface. But beyond the technical outcomes, it’s also deepened our academic relationships and helped align enterprise needs with cutting-edge research in a way that feels genuinely collaborative and industry-focused.
— Cathal O’Neill, Senior Director of Software Engineering, Rapid7
Key messages
As the Programme achieves ‘momentum equilibrium’, early stage outcomes and impacts are starting to become apparent. These include important strategic value added effects, such as the Programme’s key influence on the design of the national LASR initiative, enabling leading-edge technology development in Northern Ireland’s cyber sector, and helping to define, characterise, and connect NI’s cyber ecosystem. However, it is yet too early to evidence with rigour quantitative progress against the Programme’s five objectives – this will be a key focus of Reports 4 and 5.
From the perspective of stakeholders, the Snapshot is seen as the most visible and tangible Programme strand at present. Awareness of Technologies Hub activity is mixed, and detailed understanding of project content is limited, constraining views on how outcomes and impacts are building. Case study evidence highlights potential for significant commercial impact from projects, together with the strengthening of firms’ relationship with CSIT, and the identification of future collaboration opportunities.
On the PhD and MSc strands, participants continue to make good progress towards qualifications, with some already having graduated and a relatively low dropout rate. The number of publications involving the PhD researchers is increasing, with some evidence that these are already adding value, given the number of downloads to date. MScs who have graduated to date are pursuing a range of opportunities, with three with new employers, six undertaking further study and three with the same employer.
It is yet too early to assess achievement against the Programme’s five objectives; this noted, there is consultee concern that the New Decade New Approach target of 5,000 cyber jobs in Northern Ireland in 2030 may not be realised, which may have implications for the Programme’s own commitment to 150 jobs created. The Programme Delivery Team will want to actively monitor this, and take necessary action.
As the Programme enters its second half of activity, attention needs to turn to realising and optimising benefits, with Programme succession a key strategic issue now to start planning for.
5. Conclusions & recommendations
Purpose
This chapter summarises the key findings from this phase of the evaluation and sets out recommendations for future work, both on this evaluation and the Programme more broadly.
Summary of this report findings
Programme origins and strategic context
Since its inception in 2021, the Programme has proven prescient in anticipating the growing strategic importance of AI, cyber security, and their intersection. External developments have only reinforced this relevance, with consultees noting the Programme’s foresight, in terms of both markets and technologies. Early-stage impacts are beginning to emerge, such as its strategic contribution to the design of the national LASR initiative, support for leading-edge technology development in Northern Ireland’s Cyber sector, and efforts to define and connect the region’s wider cyber ecosystem.
Current delivery and performance
Recruitment targets have now been met across the Technologies Hub, PhD, and MSc strands. At its peak, the Hub supported eight active projects, though four of the original private sector participants have since withdrawn. One replacement has been secured, and recruitment for others is ongoing. Achieving the target of eight completed projects is likely to remain a challenge.
The MSc and PhD programmes have recruited effectively, though MSc recruitment was spread over an additional academic year. Moderate churn has occurred, as expected, but tight recruitment criteria and a limited pool of eligible candidates have made replacing dropouts difficult. Peak recruitment aligned with completion targets, leaving no buffer for attrition. While some dropout is inevitable, this could have been mitigated through over-recruitment and/or by adjusting completion targets.
The Programme has experienced underspend in some strands, but mitigations - such as advancing the capital purchase of the GPU cluster - mean full budget utilisation is now expected within the planned timeframe. The spend profile has shifted to later years, with the Technologies Hub now accounting for a larger share than originally planned, supported by budget reallocation from the PhD strand.
Case studies for this report from two Technologies Hub projects highlight strong industry-academia collaboration, with substantial knowledge-transfer benefits. The Hub’s integrated co-planning model distinguishes it from typical R&D initiatives and is valued by both companies and academics.
The MSc and PhD strands are progressing well, with some graduates already emerging and dropout rates remaining low. The PhD strand will not meet its target of 15 graduates due to two withdrawals. Academic engagement through publications and participation in conferences by PhD students are increasing, with early signs of impact based on download metrics. MSc graduates are pursuing varied paths: three with new employers, six in further study, and three remaining with their original employer.
Looking ahead: succession and strategic planning
As the Programme enters its second half, attention must shift to realising and optimising benefits. Succession planning is now a key strategic priority. Consulted stakeholders have identified the Snapshot strand as the most visible and tangible element of the Programme, while awareness of Technologies Hub activity remains mixed. Limited understanding of Hub project content, combined with the need to protect intellectual property rights around research and development, implicitly restricts the Technologies Hub’s marketability and reach. This, in turn, limits how its outcomes and impacts are perceived.
There is concern among consultees that the New Decade, New Approach target of 5,000 Cyber jobs in Northern Ireland by 2030 may not be realised, which could impact the Programme’s own commitment to creating 150 jobs. The Programme Delivery Team will need to actively monitor this and take necessary action. Future evaluation reports (4 and 5) will focus on evidencing quantitative progress against the Programme’s five objectives, which remains immature at this stage.
Key learning and recommendations (on (i) further process aspects and (ii) developing outcomes)
This second interim evaluation of the Programme highlights both the progress achieved and the ongoing challenges faced across its four strands. Building on the findings and stakeholder feedback, the following recommendations are proposed to optimise delivery and maximise impact as the Programme moves into its second half.
1. Succession planning
- As the end of the Programme’s funding starts to come into view, it is vital to begin post-Programme planning to ensure the sustainability of its model and success. This is a key issue widely recognised by consulted stakeholders. Accordingly, Queen’s, DSIT and other partners should consider the focus and aims of any rationale-based successor programme, including the potential for scaling beyond Northern Ireland and diversifying funding routes. This should explicitly consider alignment with wider strategic partnerships and programmes such as LASR and AICC.
2. Enhance programme visibility and promotion
- While recognising the commercial sensitivities inherent in R&D activities and the Programme’s subject matter, more could be done to raise the profile of the Programme both among cluster actors in Northern Ireland and more broadly across the UK. The existence, focus and subject matter are strategically significant for Queen’s, CSIT, and Northern Ireland as a whole and as such, the Programme itself could be more widely promoted. This would serve to emphasise Northern Ireland’s strengths in the sector, and the commitment of project partners to growing the sector and its talent pipeline could be instrumental in attracting foreign direct investment.
3. Strengthen strategic ecosystem relationships
- In response to the recommendation in the last report, the Programme has demonstrated strong progress this year in increasing opportunities for Programme participants and other sector actors to network and collaborate. More broadly, there are opportunities to deepen engagement with other key sector players, programmes, and institutions, particularly AICC.
- Whilst CSIT and AICC are already engaged, stronger alignment and collaboration will help build more cohesive and resilient cyber and AI ecosystems in Northern Ireland. The Cyber-AI Hub Director joined the board of AICC in 2025 and has regular engagement which is helping to ensure alignment across the two initiatives. AICC may identify and signpost companies that could benefit from deep-tech collaboration with cyber security experts provided by the Cyber-AI Hub.
4. Setting achievable and realistic targets
- A degree of churn among participants (companies and individuals) is inevitable in programmes such as this, but given targets for each strand were aligned to the number of recruits (e.g. 15 PhD candidates were recruited with the aim of achieving 15 PhD graduates), the Programme will not be able to achieve outputs as planned due to students leaving the Doctoral Training Programme (DTP). Future programmes should seek to adopt targets which reflect a degree of churn, and therefore embed some contingency. This could include different targets for recruited participant numbers and achieved outcomes; or adopting an approach of recruiting participant numbers above target outcomes.
- For the remainder of this Programme, current efforts are rightly focussed on identifying companies and projects who can deliver against the aims of the Technologies Hub, replacing those who have left the Programme to date whilst still delivering on strategic objectives.
5. Programme management and reporting
- Programme management and monitoring are much stronger than at the Initial Process Report stage, reflecting welcome progress against that report’s recommendations. This could be strengthened further by consolidating data on participants and finances by strand into a single source/document, providing a consistent version of the truth;
6. Ensuring future programmes meets sector needs
- It is important to recognise that, since the design of this Programme, advances in AI appear to be reducing demand for entry-level skills in the sector. This is a bigger issue than this Programme is able to address, but it has significant implications for growth of the sector both in the short term and over the coming years. A lack of new entrants into the sector’s labour pool now limits the availability of experienced staff in future years. DSIT should work closely with industry to consider these implications.
- Future successor programmes should also be cognisant of these issues and provide clear pathways for participants to develop the skills industry require. This could include co-design of development pathways with industry, and developing clear routes for MScs and others to progress to PhDs through the Programme, enabling them to develop the higher-level skills employers demand.
Overall, the Programme has demonstrated strong progress over the past year with evidence of impact emerging through the MVPs developed in Technology Hub projects, successful MSc completions and research outputs emerging from PhDs. Future phases of work on this evaluation will focus more specifically on measuring these outcomes and associated impacts.
Annex A: summary of technologies hub projects
| Project | Description and Progress | Achievements and Next Steps |
|---|---|---|
| ANGOKA - Device ID generation and entropy analysis using cryptographic techniques | • ANGOKA has developed a patented approach which takes multiple characteristics of a device, combines them using a cryptographic algorithm, and outputs a unique and immutable device identity (or fingerprint). • The project aims to identify the optimal combination of characteristics which will give the highest entropy for input to the fingerprint creation. • A minimum viable product for this project is still a work in progress. | • Work completed on cryptographic /mathematical modelling (100% complete) • Complete entropy exploration and testing (50% complete) • Continue work on Identity Generation Algorithm (25% complete) • Start work on chamber testing • Start work on use case and demonstrator • Expected output: New technology that Angoka could exploit across multiple products and platforms. |
| Controlsoft - Machine Learning Driven Anomaly Detection for Advanced Persistent Threats (APTs) in Industrial Control Systems | • The project aims to employ advanced machine learning (ML) techniques to model industrial systems and identify cyber-attack behaviours associated with relevant APTs, and evaluate the model’s effectiveness against such behaviour. • Controlsoft joined the Programme in March 2025. As well as finalising the collaboration agreement, the team has completed onsite training for CSIT on the data centre and developed architecture and process for training models. • A minimum viable product for this project is in progress. • ControlSoft have announced 27 new jobs in Northern Ireland | • Work completed on benchtop testbed and architecture and process for training AI models • Work completed on functional design specification for use case and data collection • Complete work on replicating the EPMS (Essential Power Monitoring System) panel • Complete work on the initial ML model • Expected output: PoC on anomaly detection specifically within security of Industrial Control System. |
| Pytilia - Context Aware Vulnerability Detection and Mitigation | • Aims to support businesses in identifying and prioritising security vulnerabilities in their networks and systems. • Progress has been made on workstreams relating to vulnerability data integration, AI/ML model development and training and monitoring and alerting systems. • A minimum viable product is still a work in progress for this project. | • Work Packages 1 and 2 (systems architecture design and vulnerability data integration) are complete. Work will continue on all other workstreams, including model development, context-aware vulnerability scanning and monitoring systems – the latter of which remains complex, despite progress. • Although the project has not led to any publications or products as yet, there is a reasonable chance that aspects around vulnerability prediction will warrant publication, and ultimately could potentially lead to a new product offering for Pytilia. • Expected output: An MVP is expected from this project. Additionally, Pytilia has gained new know-how in multiple AI technologies that it is already implementing across the business. |
| Rapid7 - AI Alert Triage | • Rapid7 underwent a period of strategic change in early 2025, leading to a new project focus on Alert Triage (AT). • R7 held the first AI AT learning and enablement session end of June, kickstarting the project following organisational change. • A first minimum viable product has been achieved, with a second still a work in progress • Rapid7 invited CSIT to meet with a new customer during a visit to Belfast, presenting on CSIT expertise and collaboration with Rapid7 in the Cyber-AI Hub. | • First output: MVP - Work package 1 yielded a valuable technological side outcome around anomaly detection. This outcome is now being protected as intellectual property (IP) and is under consideration for integration into Rapid7’s broader cloud response offerings. • The new project team is upskilling on the AI AT system, to build sufficient knowledge in order to be able to begin R&D in earnest. • The sensitivity of this project is likely will involve a new protocol between CSIT and R7. • Expected second output: Automated AI-enabled Alert Triage (prioritisation) |
| Thales - STEADY (Secure & Trustworthy Ensemble AI Systems for Real World Deployment) | • This project is working towards development of methods in how AI/ML models and AI enabled systems can be verified and made trustworthy. • The team held a three day workshop at CSIT in May 2025. • A proof of concept for this project is still a work in progress. | • Work package five, the detection of anomalous data, is now complete, and work has started on work package nine utilising The Assurance of Machine Learning for use in Autonomous systems. • Work in late 2025 will focus on performance prediction, system verification and assurance. • Expected output: A PoC demonstrating the trustworthiness of AI, with significant application across multiple safety critical sectors where assurance is essential. |
| Ampliphae - Application of AI to cyber-security of 5G mobile telecoms | • Completed development of an O RAN/ 5 G network slicing application. This was originally conceived as a vehicle for ML security testing. However, it may have commercial application for a telco operator. • Ampliphae’s IP, and innovation team, were acquired by Arqit in May 2025 and the project is now closed. | • Project closed • Output: A minimum viable product for this project has been completed prior to project closure - the development of an O-RAN/5G network slicing application. This was originally conceived as a vehicle for testing but potentially has commercial application. The Cyber-AI Hub team is in ongoing discussions with BT exploring commercial potential. |
| Nvidia – AI-based Threat Prediction and Prevention for Data Centre Security | • The project aimed to address the immaturity and novelty of artificial intelligence and model learning (AI/ML) for security purposes, aiming to reduce the computation cost and reduce the number of false positives and false negatives when using AI/ML for security. • The project aimed to deliver; testbed and traffic generation; DFP+ improvement through feature analysis and optimisation; DPU VMs; and attack classification. • Nvidia lead on this project is leaving the organisation this summer, and Nvidia does not intend to continue development on this project in the short term. | • Project closed • The project was negatively impacted by lack of access to good quality time-synchronised data across network traffic and event logs. We used commercially available off-the-shelf data collection tools which proved inadequate to the task, and this meant that the team was redirected to efforts to generate suitable data through activities including Capture The Flag which proved inefficient. • Output: Despite the difficulties, we still believe that the project has potential and we will explore other opportunities to progress this, using alternative data collections tools. • Through this project, the CSIT team developed know-how and experience, as well as links with Nvidia US West Coast team. |
| Cynalytica - ICS malware | • The project aimed to use AI/ML to develop techniques for the detection of industrial control system (ICS) malware. • Cynalytica left the Programme in 2024 having not fully engaged in the Programme | • Project closed • ControlSoft has joined the Cyber-AI Hub on an ICS project. |
| Skurio - Open Source Threat Intelligence | • The project sought the implementation of a model based on LLM to predict the classification of malware with up to 96% accuracy. • The project was paused, as the firm went into administration. | • Project closed • Output: The project achieved proof of concept for a ransomware classification model, with a completed research publication which has been accepted to The 3rd International Conference on Foundation and Large Language Models (FLLM2025), Vienna, Nov 2025. Another publication is in progress. • The project learnings have been shared with other companies as the team explores other options to progress this project. |
Annex B: consultees for this report
| Position | Organisation |
|---|---|
| Associate Professor/Senior Lecturer in AI Security | CSIT, Queen’s University Belfast |
| Strategy Lead, Laboratory for AI Security Research (LASR) | FCDO |
| Senior Software Engineer | Pytilia |
| Director | AICC |
| Senior Lecturer | Queen’s University Belfast |
| Director | Perspective Economics Ltd |
| Digital ICT Sector Lead | Invest NI |
| Head of Artificial Intelligence & Machine Learning | Innovate UK |
| Cluster Manager | NICyber |
| Cyber innovation aspects | Innovate UK |
| Software and Cyber Policy Lead | Department for Economy |
| Programme Lead for Cyber AI programme, and DSIT’s Lead for this evaluation | DSIT |
| CEO | Software NI |
| Head of Cyber Growth, Innovation and Regions | DSIT |
| Professor and Academic Director, CSIT | Queen’s University Belfast |
| Executive Director, Business Growth | Invest NI |
| Director of Operations, CSIT | Queen’s University Belfast |
| Deputy Director, CSIT | Queen’s University Belfast |
| CSIT Research Director, Programme PI | Queen’s University Belfast |
| Senior Director of Software Engineering | Rapid7 |
| Lecturer | Queen’s University Belfast |
| Technical or programme delivery role | Queen’s University Belfast |
-
Regional gross value added (balanced), ONS 2025 ↩
-
UK Innovation Survey, BEIS, 2019. ↩
-
NI Cyber Snapshot, Perspective Economics, 2025 ↩
-
This includes contributions from industry (£2.2 million) and Queen’s University Belfast (£2.3 million). ↩
-
Evaluation of the Cyber AI Hub programme - Initial Process Evaluation, 2025 ↩
-
NI Cyber Snapshot, Perspective Economics, 2025 ↩
-
Feedback from MSc and PhD students/graduates is planned to be obtained for next year’s evaluation monitoring report. ↩
-
Cyber security skills in the UK labour market 2025, Ipsos / Perspective Economics on behalf of DSIT ↩
-
Originally it was intended that Nvidia should feature as a case study for this report, but the firm’s managed withdrawal from the Programme meant this was not feasible. Given sensitivities and time constraints involving other projects, Rapid7 was selected, this to build on the case study undertaken with the firm the previous year. ↩
