Register for and manage the PSN DNS
Use the PSN DNS to continue reaching PSN services after you stop using GCF Core Services. This will save money and protect your IT systems from malware.
About the PSN DNS
The PSN DNS is provided by Nominet and gives you an alternative to the legacy domain name system (DNS) provided with GSi Convergence Framework (GCF) Core Services.
The PSN DNS uses National Cyber Security Centre’s (NCSC) Protective DNS, also provided by Nominet. The NCSC Protective DNS protects users from attacks by blocking access to potentially malicious sites identified by government, commercial and community sources.
NCSC’s Protective DNS is part of the UK government’s Active Cyber Defence programme. You can read more about how the Protective DNS fits into the National Cyber Security Strategy (page 33).
Register for the PSN DNS
Registration for the PSN DNS is currently closed.
You can manage your PSN domains after registering for the PSN DNS. The online support tool will show your organisation’s PSN domain names.
Configure your settings
The PSN DNS is hosted on the internet, and visible to internet users and PSN users. The PSN DNS uses a single view of PSN DNS data across PSN and the internet. There are a number of technical configurations you must apply to use the service.
For more detailed guidance on setting up the technical configurations, and other GCF exit technical matters, go to the PSN team contact centre, select Sign In, then Sign Up and follow instructions. You can then access technical guidance to exit GCF Core Services.
Support
Nominet provides support to public sector and commercial organisations’ technical administration teams. Nominet does not provide direct support to individual end users. End users should contact their own IT service desk for all support requests.
You can use the online support tool to:
- register to use the DNS
- raise change requests to manage your organisation’s PSN domain names
- raise operational issues with the DNS
- ask questions about the DNS
- monitor the status of the DNS
You can use the online support tool or email the support team at dnssupport@nominet.uk.
Nominet provides routine support from 8am to 6pm Monday to Friday.
Report urgent requests, incidents or problems by calling 01865 332 277. This phone line provides 24-hour support, 7 days a week and should be used when:
- your organisation experiences a loss of service
- you need to request an urgent change to a domain to ensure continuation of service
Service levels
The PSN DNS is designed to be highly reliable and available, geographically diverse and low latency. Each node connects directly to multiple service provider networks for a fast and reliable service.
The stated peak resolution volume in queries per second can be handled even in the event of multiple simultaneous site failures. There are no single points of failure to DNS resolution. The PSN DNS:
- has an over-provisioned diverse internet transit connection capacity so there’s suitable bandwidth
- manages incoming queries to discard wrong or malicious requests
- protects against DDoS attacks upstream
The PSN DNS provides the following performance and availability.
| Attribute | Performance |
|---|---|
| Resiliency and disaster recovery | Geographic with real-time replication |
| Service availability | >99.999% including all periods of maintenance |
| Response time from nameserver edge for cached response | <10ms |
| Time to respond to customer requests | Less than 1 hour (telephone), average 4 hours (email and online support tool) in office hours |
| Supported features | IPv4, IPv6, DNS, DNSSEC |
PSN DNS terms of use
By subscribing to the PSN DNS you agree to the following terms of use.
- The PSN DNS is provided ‘as is’ free to users by arrangements made with GDS.
- Nominet and GDS do not provide any warranties as to minimum service standards and functionality.
- Nominet does not accept any liability for any loss of service or functionality.
- You must not use the PSN DNS for any unlawful purposes.
- Nominet monitors DNS queries and analyses DNS traffic. Nominet processes and shares this data with GDS and other government organisations including NCSC, to help check that the DNS is running smoothly, improve the DNS, and detect threats and anomalous DNS traffic patterns.
- Nominet will attempt to block access to IP addresses and domain names which are believed to be associated with malware or other threats. However, Nominet does not guarantee that the DNS will effectively block all malicious sites.
- Your end users may also be inadvertently blocked from accessing sites which carry no risk.
- Nominet is not responsible for any third-party content or material which you may be able to access on the internet via the DNS.
- Both Nominet and your organisation can terminate your use of the PSN DNS services at any time, with one month’s notice.
- To continue using the PSN DNS, your organisation’s PSN-connected environments must maintain PSN compliance.
Technical overview
The diagram shows how the PSN DNS uses:
- internet access points for PSN users
- NCSC’s Protective DNS
- the PSN DNS authoritative nameserver
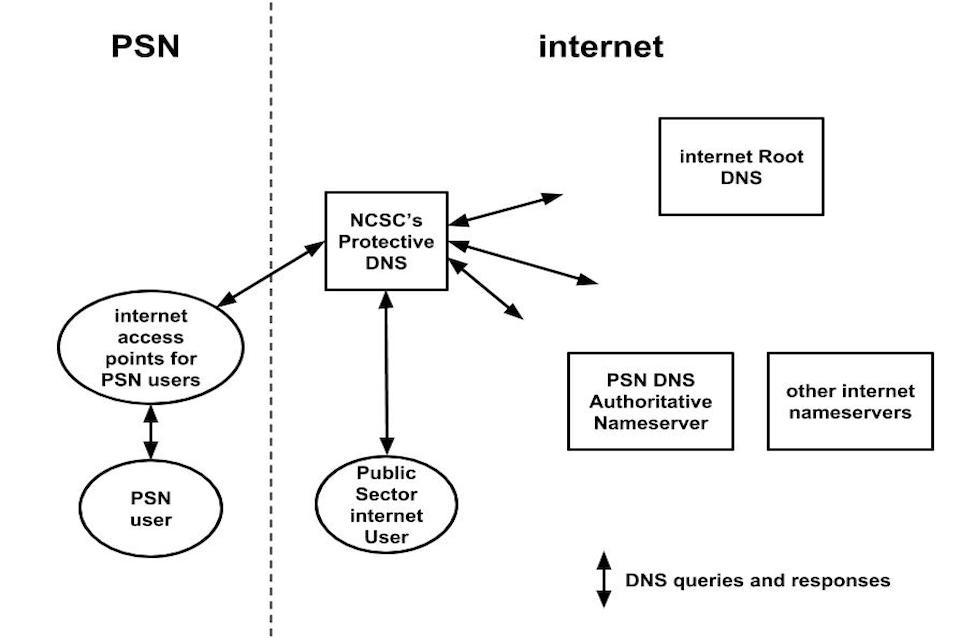
A diagram showing how the PSN DNS works
You can access the PSN DNS from one of several IP addresses within PSN. These IPs connect directly to more than one Direct Network Service Provider (DNSP) network for a fast and reliable service. You’re dependent on your PSN network service provider to reach the DNS. The DNS connects only to PSN Assured networks. If you’re connected to a PSN Protected network, you’ll be able to reach the DNS because PSN is flattened.
Updates to this page
-
PSN DNS registration is currently closed. We will update this page when it reopens.
-
We have changed this guidance to reflect the launch of the PSN DNS.
-
First published.